§ 01
Overview
Who: A two-person research team at BCIT — Austin Webber and Kaiden Koran — as part of the FSCT 8590 Network Exploits and Vulnerabilities course, with test devices operated under fictional personas (John Titor, Ryoma Echizen, Dean Winchester, Sam Winchester).
What: A multi-vector forensic investigation into Snapchat, targeting the recovery of disappearing messages, media artefacts, and account metadata across both Android and iOS platforms.
When: Controlled study window ran from January 22 to February 19, 2026.
Where: Conducted in an isolated BCIT lab environment. All devices were test accounts on a segregated network with no connection to authentic user data or Snapchat's production infrastructure.
Why: Snapchat is built around ephemerality — messages vanish by design. This project examined whether forensic techniques can recover meaningful evidence despite that design, and where the ceiling of each acquisition method falls.
How: Three simultaneous approaches were pursued: (1) network-layer MITM interception of QUIC/TLS 1.3 traffic; (2) full file system and logical extraction on Android devices; (3) iTunes backup analysis and Keychain extraction on iOS devices. All findings were processed through Magnet AXIOM and Cellebrite Physical Analyzer.
§ 02
Lab Setup
The MITM environment was built on a dedicated Linux host acting as a wireless access point. All test devices connected through this host, routing their traffic through mitmproxy for interception. SSL pinning — Snapchat's primary defence against traffic inspection — was bypassed on Android devices using Frida runtime instrumentation injecting a custom script to disable certificate validation at runtime.
Test devices:
- ASamsung Galaxy A8 (rooted) — "Ryoma Echizen"
- BSamsung Galaxy S8 (non-rooted) — "John Titor"
- CiPhone XS (iOS backup) — "Sam Winchester"
- DiPhone 13 (iOS backup) — "Dean Winchester"
Packet captures (PCAP) were collected using Wireshark on the Linux host over the duration of the study window, capturing all Snapchat-bound traffic for later analysis.
§ 03
Network Analysis
Snapchat uses QUIC over UDP with TLS 1.3 for all media and message traffic. The combination is effectively opaque to a MITM observer: even with Frida bypassing Android's SSL pinning, Snapchat's additional application-layer certificate pinning (Fidelius) prevented content decryption at the network level.
This metadata is not trivial — it establishes connection timelines and can corroborate device-level evidence when cross-referenced with SQLite artefacts recovered from storage. It cannot, however, stand alone as evidence of content.
§ 04
Device Extractions
Android — FFS vs. Logical
The access level of an Android extraction is the single most decisive factor in
Snapchat artefact recovery. On the rooted Galaxy A8, a Full File System (FFS)
extraction via ADB and Magnet AXIOM produced near-complete results: the
Snapchat artefact database (arroyo.db), cached media fragments, account
metadata, and partially recoverable deleted message records were all accessible.
On the non-rooted Galaxy S8, logical extraction yielded essentially nothing actionable — Snapchat's sandbox prevents logical tools from reading its data directory without elevated privileges. Additionally, OEM Unlocking was unavailable on this Canadian variant.
| Artefact | FFS (Rooted A8) | Logical (S8) |
|---|---|---|
| Chat records (arroyo.db) | Recovered | Not accessible |
| Cached media | Recovered | Not accessible |
| Account metadata | Recovered | Not accessible |
| Deleted records | Recovered | Not accessible |
iOS — Backups and Keychain
iTunes encrypted backups were analysed for both iPhones using Magnet AXIOM and Cellebrite Physical Analyzer. Snapchat stores minimal data in standard backups by design — chat content and media are excluded — but several high-value artefact categories were recovered.
- 1InteractionC database — conversation timeline records, first-contact events, and interaction counts across the study window.
- 2Keychain artefacts — account activation timestamps (fideliusTransferableDeviceGraph), session tokens (SCOneTapLoginKeychainKey), establishing precise account chronology.
- 3EXIF location data — a screenshot taken on the iPhone 13 at 3:36 AM on February 13 contained GPS coordinates placing the device in Maple Ridge, BC.
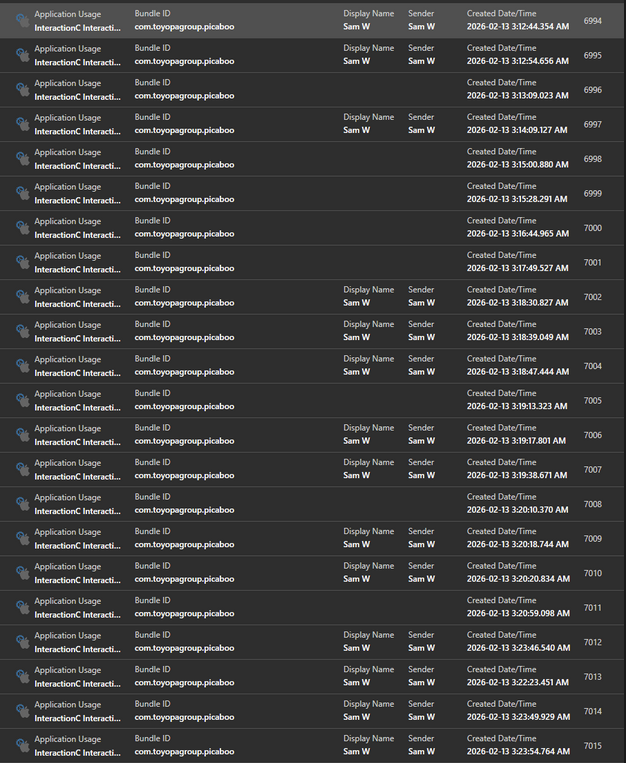 Figure 2 — InteractionC Timeline Visualisation
Figure 2 — InteractionC Timeline Visualisation
§ 05
Conclusion
Despite Snapchat's design philosophy of disappearing content, this study confirmed that significant forensic evidence persists — the question is whether investigators have the access level and tooling to reach it.
Key Outcomes
- 1Snapchat's QUIC + TLS 1.3 network stack effectively defeats MITM content interception; network analysis provides metadata, not message content.
- 2Android access level is decisive: FFS extraction from a rooted device yielded near-complete Snapchat artefact recovery; logical extraction on a non-rooted device yielded nothing actionable.
- 3iOS encrypted backups provide valuable metadata — account timelines, interaction records, location data — but do not expose chat content without a full file system acquisition.
- 4Ephemeral data persists. The gap between what Snapchat's design intends to erase and what forensic tools can recover is substantial, and is gated primarily by acquisition method.