§ 01
Overview
This project was a Year 1 final deliverable for BCIT's CISA program, structured as a proposal response to a simulated client — Energy Connections Inc. (ECI). The brief required designing and implementing a fully redundant, secure, multi-site campus network with centralised identity management and backup server infrastructure.
ECI allocated four routers and four switches across two sites. The network had to be operational 24/7, with Linux servers providing backup services and a pre-configured Active Directory domain structure managing all users and computers.
End Goals
- 1Full redundancy for all networking devices and end device uplinks.
- 2Data drive redundancy via RAID 5 on Linux servers.
- 3Full connectivity between local sites and the ISP via GRE/IPsec tunnels.
- 4Active Directory domain structure managing users, computers, and GPO enforcement.
- 5Security measures across Layer 2 and Layer 3 to mitigate unauthorised access.
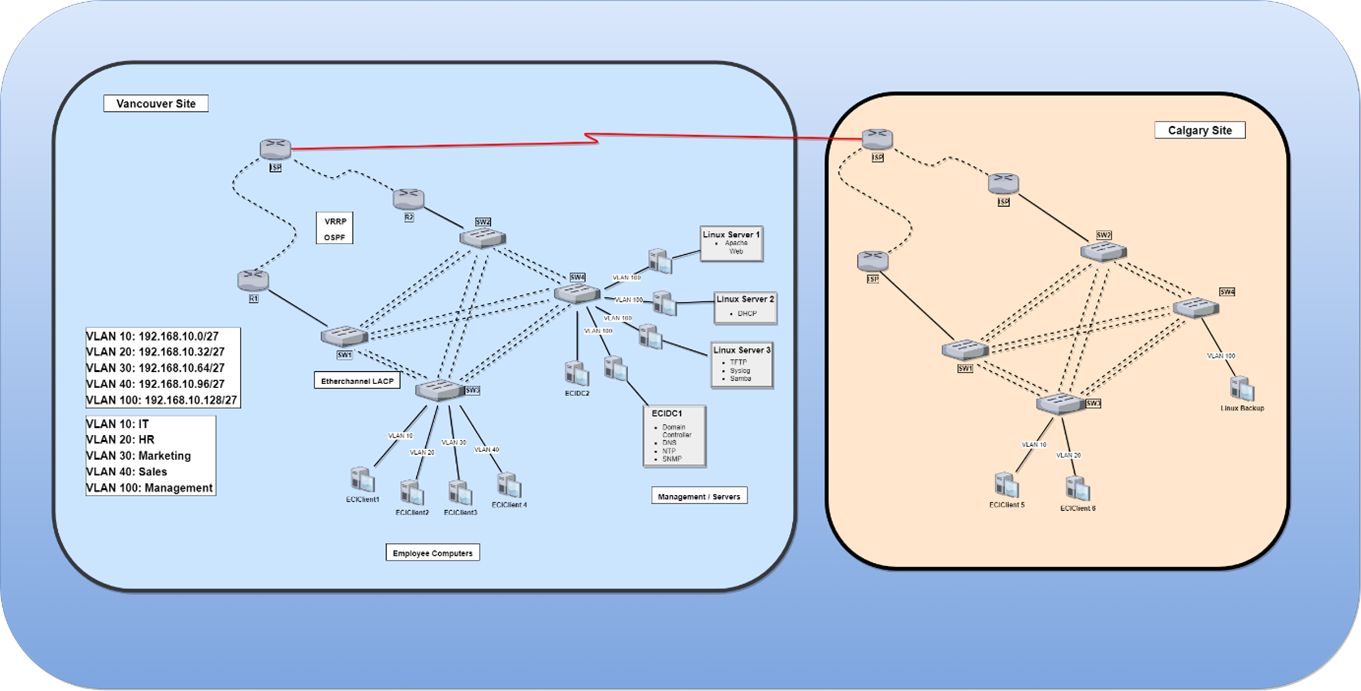 Figure 1 — ECI Logical Topology
Figure 1 — ECI Logical Topology
§ 02
Networking
Redundancy — Routers (VRRP)
Virtual Router Redundancy Protocol (VRRP) is deployed across two Layer 3 routers sharing a single virtual IP address. If the active router fails, the standby assumes the virtual IP immediately with no manual intervention required. VRRP is an open standard, allowing interoperability between Cisco and non-Cisco devices.
Redundancy — Switches (EtherChannel + RSTP)
EtherChannel in LACP mode bundles multiple physical switch-to-switch links into single logical port-channels across all four Layer 2 switches. If one physical link fails, traffic redistributes across the remaining members without losing the channel. Rapid Spanning Tree Protocol (RSTP) runs alongside EtherChannel to block redundant ports and prevent broadcast loops, while converging significantly faster than legacy STP.
Site-to-Site Connectivity (GRE over IPsec)
Inter-site traffic is secured through GRE tunnels over IPsec, providing encrypted point-to-point communication between the Vancouver and Calgary sites through the ISP. OSPF neighbour adjacency is formed across the tunnels, allowing routes to propagate automatically between sites without static configuration.
IP Services
- DHCPRouters assign IP addresses dynamically to all end devices by department VLAN. Linux DHCP server acts as hot-swap backup if the router DHCP service fails.
- OSPFDynamic routing across all routers. Neighbour authentication prevents unauthorised routers from joining the routing domain.
- NATConfigured on border routers to translate internal VLAN addresses for internet access.
- SyslogAll routers and switches send log messages at Warning level and above to the centralised Linux TFTP/Syslog server.
§ 03
Security
Security is implemented at both Layer 2 and Layer 3. Employee computers are segmented into department VLANs — a breach in one VLAN cannot directly reach another. Servers and the management workstation are isolated on a dedicated switch.
Layer 2 Hardening
| Mechanism | Purpose |
|---|---|
| Dynamic ARP Inspection | Validates IP-to-MAC bindings; blocks ARP spoofing/poisoning attacks. |
| DHCP Snooping | Permits only trusted DHCP servers to issue addresses; prevents rogue DHCP attacks. |
| Port Security | Limits the number of MAC addresses per port; locks out unauthorised devices. |
| Root Guard | Prevents unauthorised switches from winning the STP root election. |
| BPDU Guard | Disables ports that receive unexpected BPDU frames (protects against rogue switches). |
| Shutdown Unused Ports | All unused switch ports placed in a Parking Lot VLAN and administratively shut down. |
Layer 3 Hardening
| Mechanism | Purpose |
|---|---|
| SSH | All device management traffic encrypted; Telnet disabled. |
| Access Control Lists | Filters inter-VLAN and WAN traffic to enforce least-privilege access between departments. |
| Routing Authentication | OSPF neighbour authentication prevents unauthorised routers from participating in the routing process. |
| GRE over IPsec | Encrypts all inter-site traffic traversing the ISP. |
§ 04
Windows Server & Active Directory
Two Windows Server 2022 Domain Controllers (ECIDC1, ECIDC2) provide centralised
identity management across all sites under the domain eci.com. All client
machines (Windows 11) are domain-joined and receive their configuration through Group Policy.
AD DS Structure
- OUsOrganisational Units defined by site (Calgary, Montreal, Toronto, Vancouver) and by department (IT, HR, Marketing, Sales).
- Users80+ domain accounts created, assigned to department groups, and mapped to site OUs.
- GroupsSecurity groups per site (ECI_Calgary, ECI_Vancouver, etc.) and per function (IT, HR, Sales, Marketing) for granular permission management.
- NTPDomain Controller acts as Stratum 2 NTP source; all client PCs synchronise time from DC.
- SambaInteroperability between Windows and Linux hosts — Windows clients can access shared directories on Linux servers.
Group Policy (Key Policies)
| Policy | Setting |
|---|---|
| Password History | 10 passwords remembered |
| Maximum Password Age | 60 days |
| Minimum Password Length | 12 characters |
| Account Lockout Threshold | 10 failed attempts |
| Account Lockout Duration | 30 minutes |
| Audit Logon Events | Success and Failure |
| Guest Account | Disabled |
| Control Panel Access (Non-Admins) | Prohibited |
| Command Prompt (Non-Admins) | Disabled |
| PowerShell (Non-Admins) | Disallowed via Software Restriction Policy |
| Interactive Logon Message | "Only authorized ECI Domain users are permitted…" |
| LAN Manager Hash | Not stored on password change |
| Anonymous SAM Enumeration | Blocked |
§ 05
Linux Services
CentOS Linux servers provide redundant infrastructure services alongside Windows — a backup layer that remains operational if Windows services fail or become unavailable.
Services Deployed
- DHCPHot-swap backup DHCP server. If the router-based DHCP service ceases, the Linux DHCP server activates and continues issuing addresses to end devices.
- TFTPTrivial File Transfer Protocol server — stores router and switch configuration backups, and supports firmware updates and network booting.
- SyslogCentralised log collection from all network devices (routers, switches). Configured to capture Warning level and above for incident monitoring.
- ApacheWeb server hosting an internal site accessible to domain users; supports URL rewriting, logging, and access control.
- RAID 5Multiple physical disks combined into a single logical volume with distributed parity — provides data redundancy and read performance gains. A single disk failure does not result in data loss.
- SambaFile sharing bridge between Linux and Windows — Windows clients mount Linux-hosted shares as network drives through the domain.
§ 06
Outcome & Challenges
Challenges & Solutions
-
Networking
DHCP was assigning addresses to statically-configured routers.
Fix:
no service configon the router, save, and reload. - Networking LAN devices could not ping the ISP. Fix: Confirmed gateway of last resort was correctly pointed toward the ISP interface.
- Networking Site-to-site LAN communication failed across the GRE tunnel. Fix: OSPF neighbour adjacency was misconfigured — correcting the network statements on both tunnel endpoints resolved the issue.
- Windows Blending virtualisation with physical hardware caused unexpected IP conflicts. Fix: Static IP assigned to the host machine on its dedicated VLAN; domain-joined VMs obtained addresses via DHCP.
- Linux No standardised procedure for CentOS services — distribution differences required extensive testing. Fix: Iterated configurations in a virtualised environment using snapshots as rollback points.